Researchers manage to bypass Microsoft’s EMET zero-day protection
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
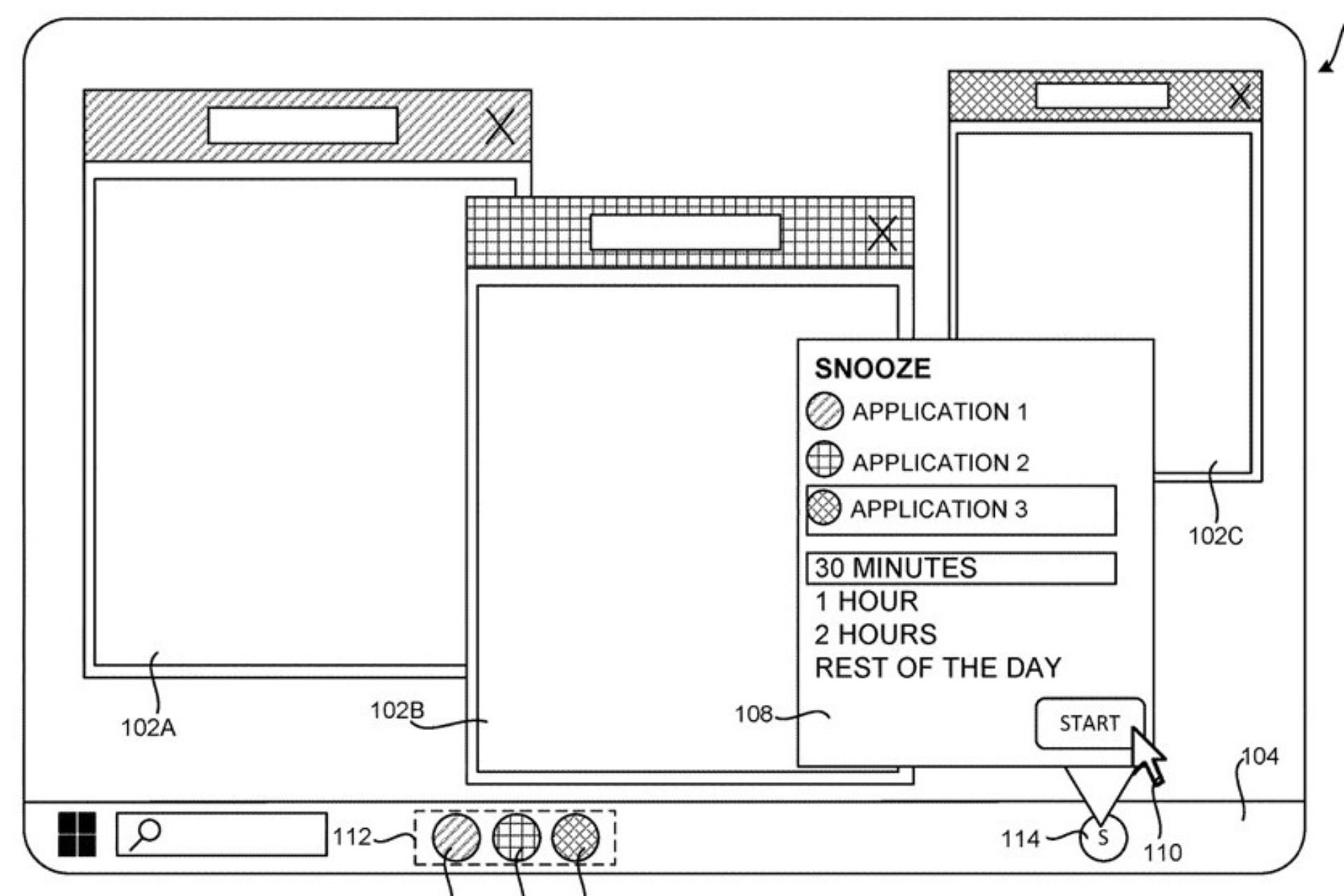
A team of researchers from security firm Bromium Labs has managed to produce code that bypasses Microsoft’s Enhanced Mitigation Experience Toolkit (EMET) software. This security tool is supposed to offer protection against zero-day attacks, and there are fears that the same technique could be used by malicious hackers to get around security and install malware.
A study by Bromium Labs set out to “gauge how difficult it is to bypass the protections offered by EMET” and included a real-world attack scenario. The lab came to the conclusion that “technologies that operate on the same plane of execution as potentially malicious code, offer little lasting protection”.
While the study focused on EMET, similar techniques could be used to bypass other comparable security system — which Bromium Labs refers to a “userland protections” — and highlights the importance of selecting the right type of security
The bypass affected EMET 4.1, and it is not clear whether or not Microsoft will be able to patch hole for the next release. EMET 5.0 Technical Preview has just been released — however, Bromium Labs have suggested that many of the weakness are too deeply ingrained to be easily address:
“The bypasses leverage generic limitations, and are not easily repaired.”
But companies who rely on EMET will undoubtedly be concerned by Bromium Labs’ claim that “yes, we found ways to bypass all of the protections in EMET.” The group points out that the research was made available to Microsoft before publication.