How to Password Protect Zip Files in Windows 11 [3 Tips]
Secure your zip folders with password protection
5 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- Password-protecting your zip files helps prevent unauthorized parties from accessing your information.
- To password-protect zip files in Windows 11, you'll need a third-party app since the operating system doesn’t ship with an in-built tool.
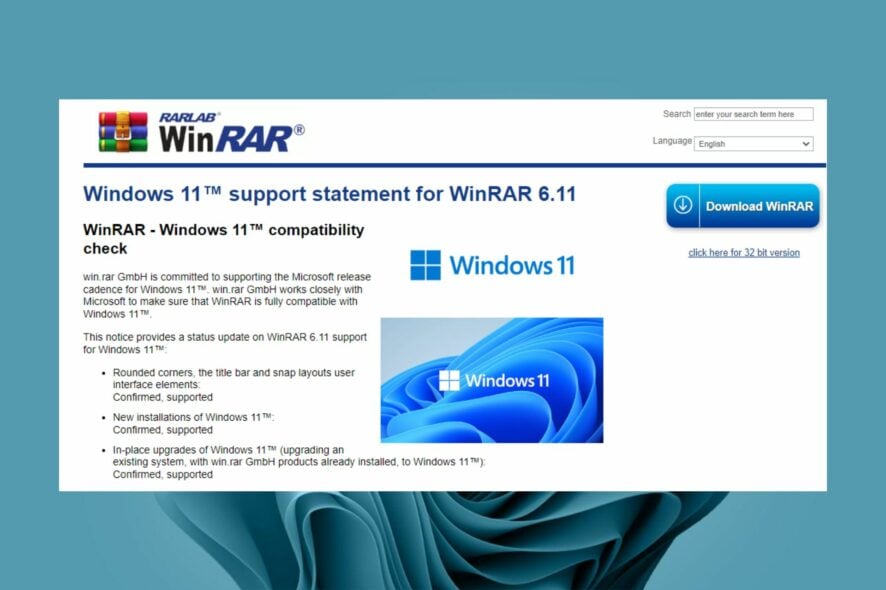
- Luckily, with open-source programs like WinRAR, you can enhance the security of your zip files in Windows 11.
Most people make use of zip support to compress their files with the aim of freeing space on their hard drives and archiving non-essential files. It also provides a great medium for users to send photos and videos through the web.
And while Windows 11 ships with native support to zip and unzip files, it does not allow users to password-protect these files, at least not natively. However, there are several open-source alternatives that you could use to password-protect your files in Windows 11.
Why can’t I password-protect a folder in Windows 11?
It should be noted that Windows 11 does not have a feature that allows users to protect a folder using a password. This is mainly because your account is already protected, which is why you need to enter a passcode every time you want to turn on your device.
Other reasons include:
- Lack of administrative privileges – You do not have administrative privileges for your PC or device where you want to perform this task.
- No built-in tool – Windows does not have a feature that allows you to password-protect your folders.
Whereas these reasons may prevent you from securing your files, if you want to add an extra layer of security to a folder in your device and password protect it, you can leverage the BitLocker and virtual drive features to create a drive that you can now secure using a password.
There might be instances where you are unable to activate BitLocker in Windows 11, so check out our article to fix it.
Although Windows doesn’t have a built-in feature that allows you to password-protect your files, you may wonder whether you can password-protect a zip file. The answer is Yes. You can encrypt your files, but if someone has access to your user account, they may be able to access the files.
To offer all-rounded protection, you must be ready to download third-party programs to enhance the security of your file. There are several options, such as WinZip, WinRAR, and 7-Zip, that will help you achieve this feat.
How can I password-protect zip files in Windows 11?
Before you password protect your zip files, ensure you check the following:
- Verify that you are using an account with administrator privileges to the zip files you want to secure.
- Ensure that your device is malware free.
1. Use WinZip
- Navigate to your browser and download and install WinZip on your PC.
- Click Create/Share on the top options.
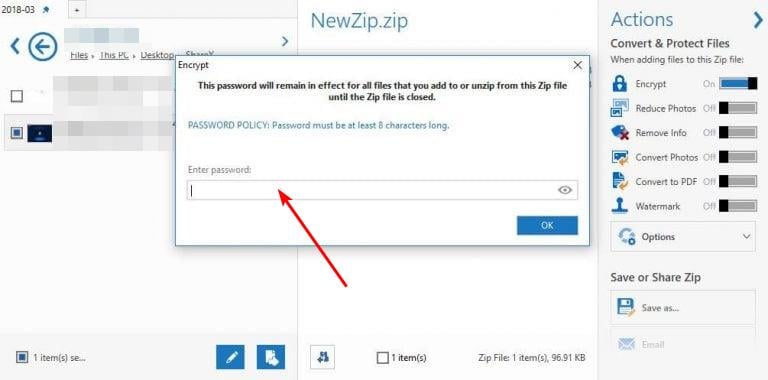
- Activate the Encrypt option in the right ACTIONS menu.
- Place your file into the NewZip.zip center space.
- The set your password window will appear.
- After setting your password, you also will need to activate the encryption setting.
2. Use 7-Zip
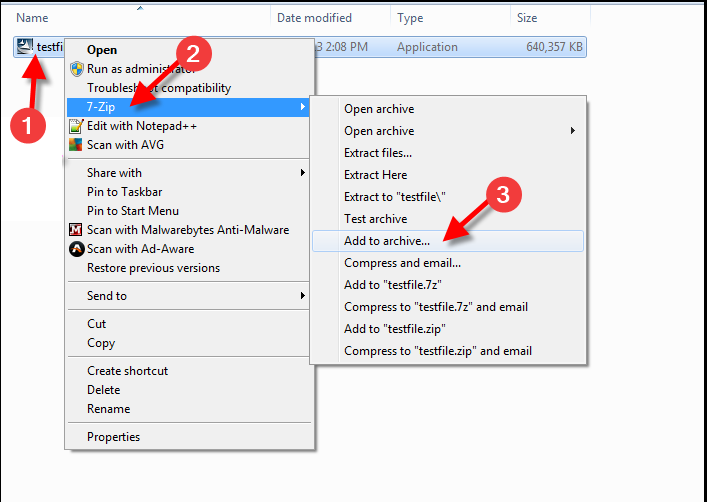
- Navigate to your browser and download 7-Zip on your Windows PC.
- Press the Windows + E keys to launch File Explorer, then find and select the file you want to zip.
- Right-click on the file and select the 7-Zip option, then select Add to archive.
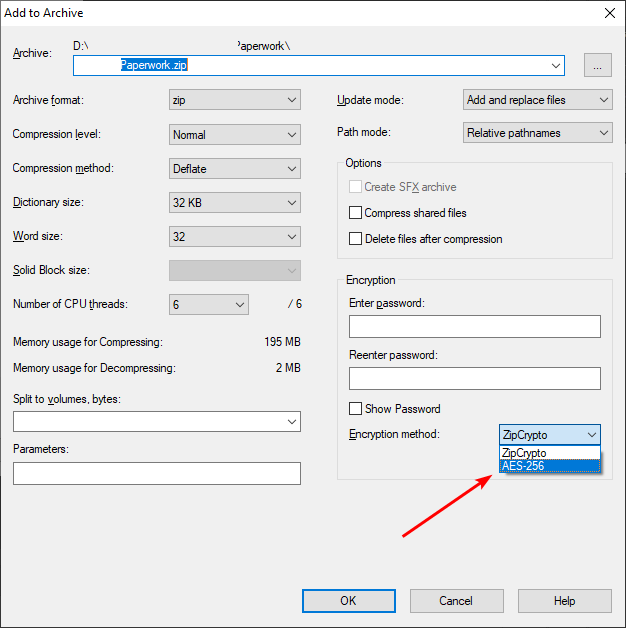
- In the new window, head to the Encryption section and create a password to enter in the Enter Password field followed by the Re-enter Password field.
- Set the Encryption method to AES-256, then click on OK to password-protect your zip file.
As you have noticed, 7-Zip is fairly easy to use and it comes with industry-standard AES 256-bit encryption.
3. Use WinRAR
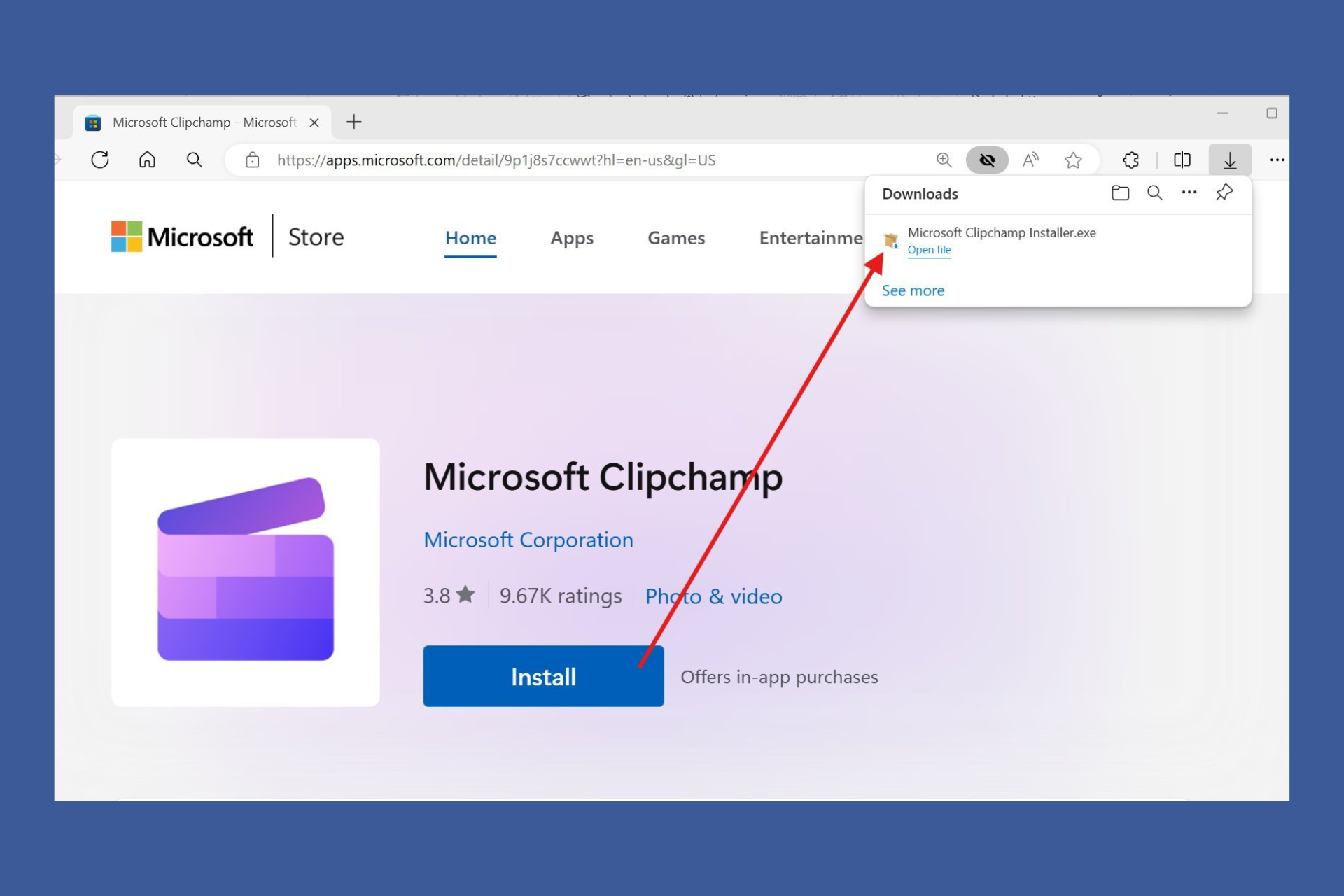
- Navigate to your browser and download and install WinRAR on your PC.
- Press the Windows + E keys to launch File Explorer, then find and select the file you want to zip.
- Right-click the file and click on the WinRAR option, then select Add to archive.
- Head to the Archive format section and select ZIP.
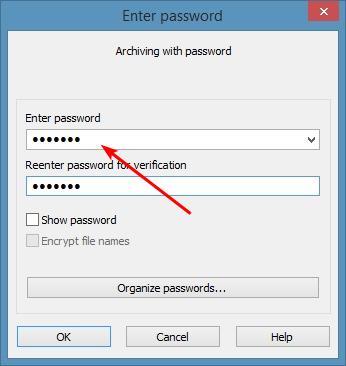
- Click on the Set password button.
- Create a password, type it in the Enter password field, then retype it in the Reenter password for verification field and finally, click on OK to zip your file.
Can you password-protect files in Windows 11?
Windows 11 features a built-in tool called BitLocker that lets users password-protect their files, thus preventing unauthorized access as well as accidental deletion. However, it should be noted that the user must be using the Windows 11 Pro or Enterprise edition.
The above methods will help you keep your information safe from unauthorized users. In some instances, you may find that you can’t extract a zip file on Windows 11, be sure to check out our expert guide on how to resolve this issue.
If you have been denied access to a certain file, we also have an article to help you bypass this issue and view the folder. You might also be interested in password-protecting compressed folders in Windows 10, we have a guide for that too.
Let us know if you could password-protect your zip files in Windows 11 using the methods listed above in the comment section below.