Microsoft confirms Secured-core PCs are better protected from “Thunderspy” Thunderbolt vulnerability
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
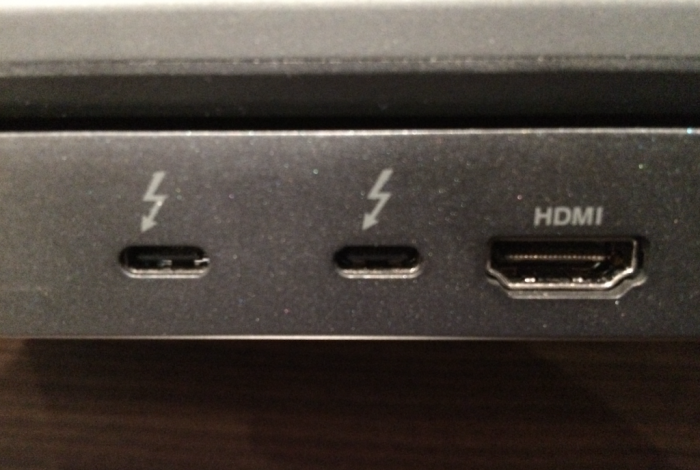
A couple of days ago, researchers at the Eindhoven University of Technology disclosed a critical vulnerability in Intel’s Thunderbolt technology labelled “Thunderspy.” According to the researchers, pretty much all PCs with a Thunderbolt port built before 2019 are vulnerable, though exploiting Thunderspy requires having physical access to PCs.
Thunderspy is considered by the researchers as a design flaw that can’t be fixed by software updates, making silicon redesign mandatory. Consequently, the only way to fully protect your PC against Thunderspy attacks is to disable the Thunderbolt controller entirely in UEFI (BIOS), though that’s probably a bit extreme considering all the benefits brought by Thunderbolt 3.
It’s not all bad, though: According to the researchers, PCs that support Kernel DMA Protection (available in systems purchased in or after 2019) are better protected from this Thunderspy vulnerability. Microsoft confirmed this yesterday in a blog post about its custom Secured-core PC architecture, which the company introduced last fall:
Secured-core PCs ship with hardware and firmware that support Kernel DMA protection, which is enabled by default in the Windows OS. Kernel DMA protection relies on the Input/Output Memory Management Unit (IOMMU) to block external peripherals from starting and performing DMA unless an authorized user is signed in and the screen is unlocked.
This means that even if an attacker was able to copy a malicious Thunderbolt firmware to a device, the Kernel DMA protection on a Secured-core PC would prevent any accesses over the Thunderbolt port unless the attacker gains the user’s password in addition to being in physical possession of the device, significantly raising the degree of difficulty for the attacker.
The list of Secured-core PCs already includes various devices from Dell, HP, Lenovo and even Microsoft’s Surface Pro X. It’s also worth noting that Microsoft never implemented Thunderbolt in its Surface devices so far, and the company specifically highlighted Thunderbolt’s security risks in an internal video that leaked last month.