Microsoft cautions customers about phishing attacks by Russian hackers
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

Microsoft recently revealed that they had identified a malicious attack. The attack is closely linked to Russian-based hackers as the objectives behind it seem to favor them. SEABORGIUM hacker group is said to be behind this attack, and Microsoft has further indicated that they are currently investigating the matter while they try to trace their digital footprint in their servers to identify any loopholes that could further subject them to susceptibility.
Microsoft Threat Intelligence Center has been closely following the moves the hacker group has been making since 2017 and established a pattern. Through constant impersonation and rapport building with targeted parties, they are able to intrude and access credential information.
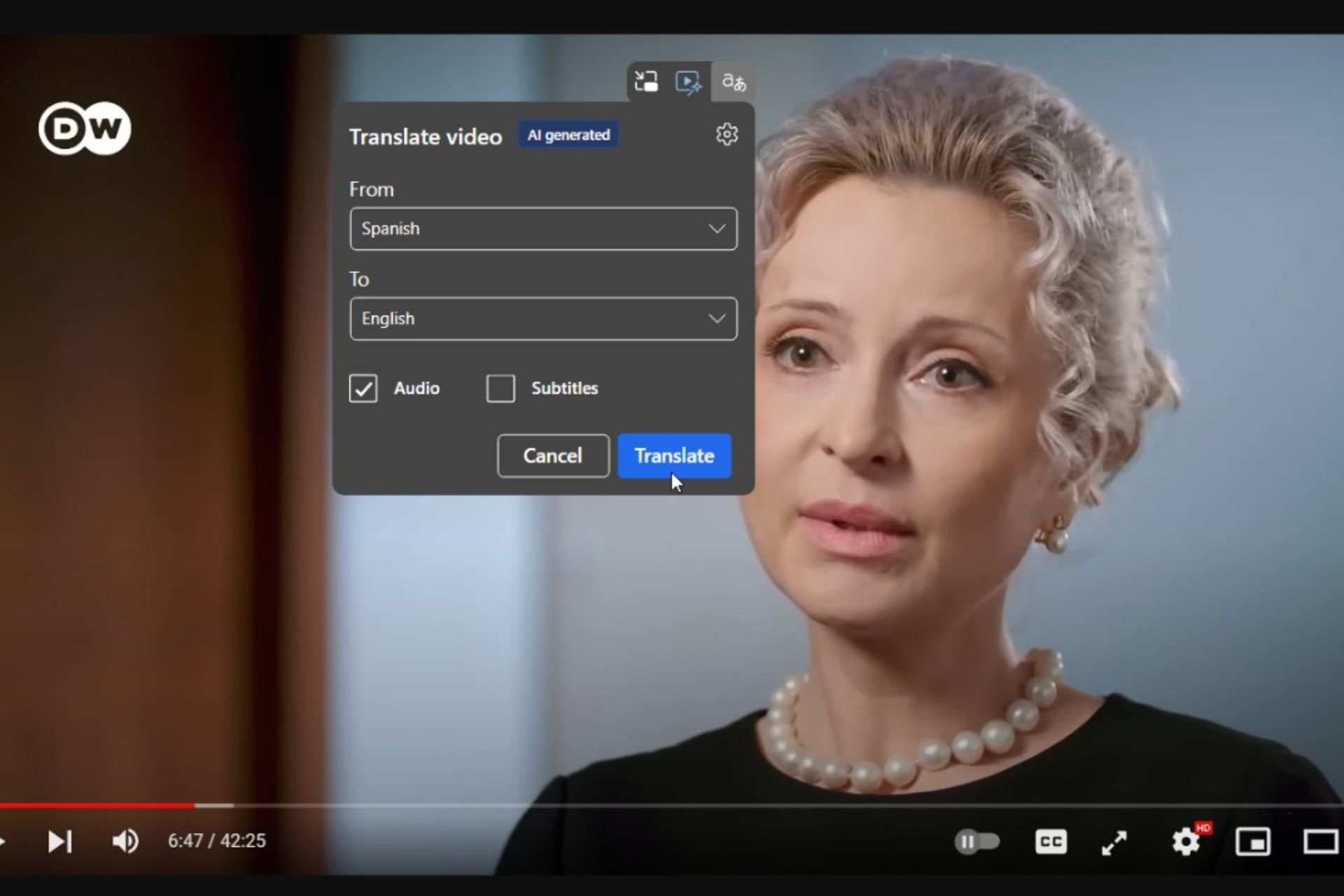
Microsoft was able to identify the challenges posed by SEABORGIUM’s infiltration especially in OneDrive thus allowing (Microsoft Threat Intelligence Center) MSTIC with all the necessary information that would allow them to salvage the situation as they already had identified the affected customers.
MSTIC partnered with abuse teams in Microsoft to disable accounts used by the actor for reconnaissance, phishing, and email collection. Microsoft Defender SmartScreen has also implemented detections against the phishing domains represented in SEABORGIUM’s activities.
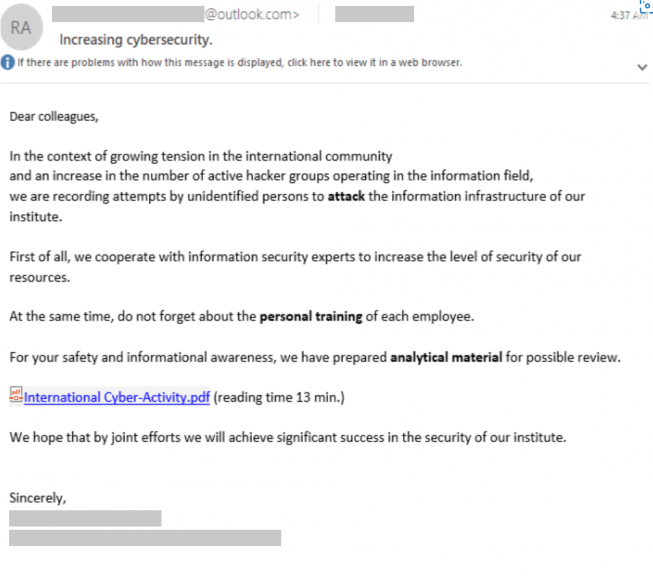
Here’s an example of how the hacker group sends out emails impersonating the lead of an organization to unsuspecting members with the aim of infiltrating their system.
Microsoft has further discovered a couple of avenues that the hacker group uses among them is including a URL directly to the body of their phishing email, a PDF file attachment that contains a URL, and OneDrive link to a PDF file that contains a URL.
Once a user clicks on the URL, they are automatically redirected to an actor-controlled server hosting a phishing framework which as observed by Microsoft often attempts to bypass automated browsing and detonation by fingerprinting browsing behavior. On the final page, the user is prompted to key in their credentials as the platform mirrors the sign-in page of the organizations. Upon completion, the attackers gain access to your account.
Microsoft has gone ahead and provided detailed information highlighting how their customers can avoid falling victims to these malicious attacks. Microsoft’s digital event held yesterday on Microsoft Security and ransomware touched on numerous ways that users can deal with these malicious attacks.