The Hows and Whys of Windows 10 telemetry settings
5 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

If the Windows 10 privacy critics are Microsoft’s worst nightmares, then ZDNet’s Ed Bott is its Sandman. As an accomplished technology writer and long-time Microsoft watcher, Bott has taken upon himself the nerve-wracking task of finding facts about Microsoft and Windows 10 to contend with the various criticisms thrown at the OS regarding privacy, ever since its introduction last year.
While Bott’s many other pieces have been responsive to sometimes ridiculous unfounded claims by tech bloggers about how Windows 10 collects telemetry data, the man seems to have finally had enough and decided to take the initiative in his newest article on ZDNet. The article provides an in-depth look at how telemetry works in Windows 10 and the data collected, drawn from Bott’s own testing and research. The information is both fascinating, highly technical, and well-arranged into the what, how, where and why.
Telemetry features aren’t unique to Microsoft and there’s nothing particularly secret about them. They’re part of a larger trend in the software industry to collect and analyze event data as part of a shift to data-driven decision making.
First of all, Bott explains how Microsoft defines telemetry, which is “system data that is uploaded by the Connected User Experience and Telemetry component,” or the Universal Telemetry Client (UTC) service, all to know what’s wrong with Windows and makes it continually better. The telemetry data also takes a very small part of the traffic between Windows and many Microsoft servers, to dispute the ridiculous numbers often cited by some network analysis online.
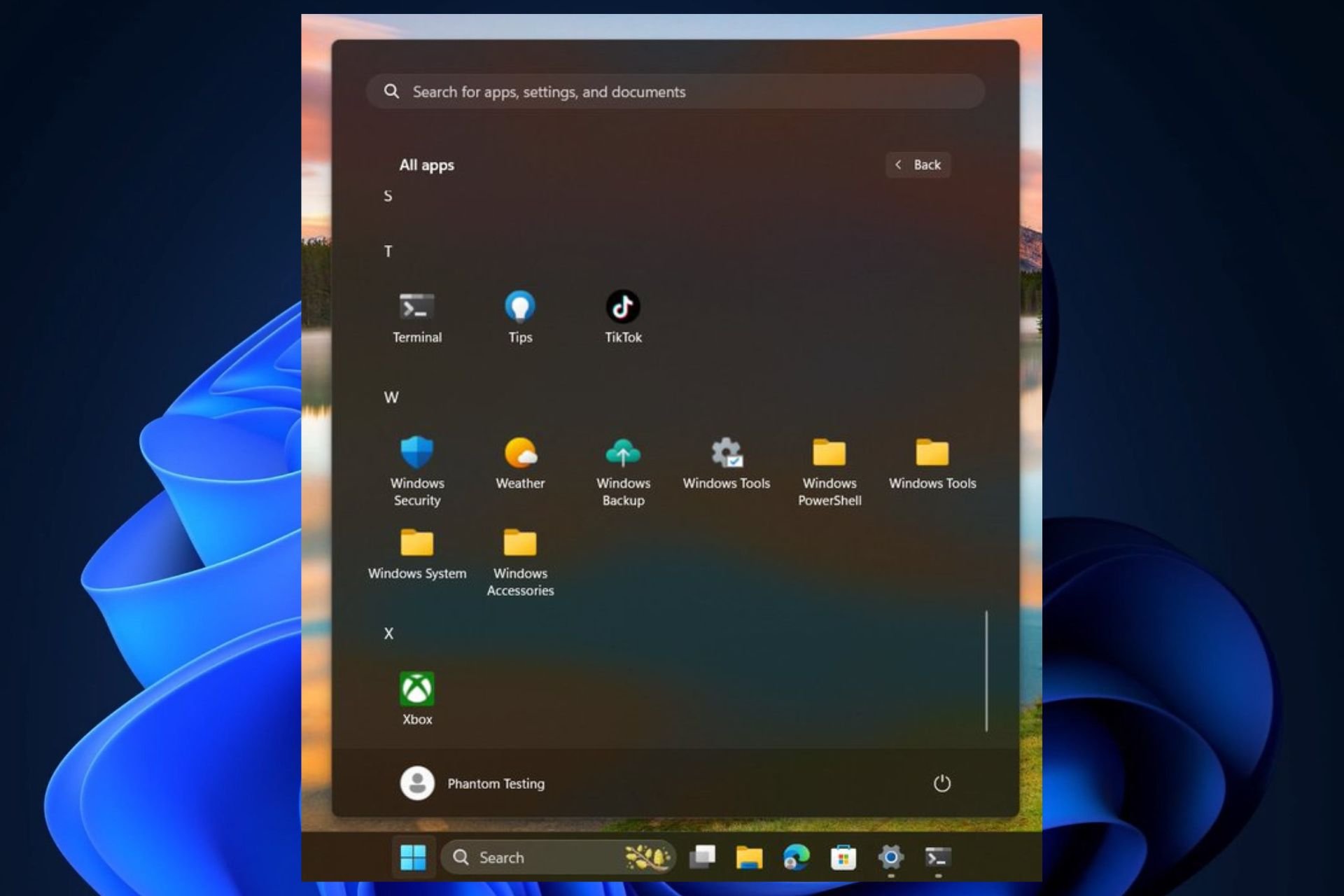
The UTC service that works with telemetry goes under the name DiagTrack and utcsvc, and can easily be found in the Services console of Windows 10.
Watching the service activities for days using its process ID obtained from Windows Task Manager, Bott found that DiagTrack only does an initial performance measurement and checks the content of four log files every 15 minutes; in other words, exactly what’s described in Microsoft’s documentation. Each data transmission is very small (we’re talking single-digit kilobits) and is only run a few times per hour on AC power and non-meter network (once every four hours on battery and none on metered network).
There are four levels of telemetry collections, which Microsoft has provided in a neat diagram along with what is collected. Further information can be found at TechNet’s full description. The gist, however, is that really concerned people totally have the choice to set the level to “Basic”, which disallows even crash dumps from being sent. The only lower level, Security, will actually disable Windows Update, so it’s not recommended unless for organization with special needs and the infrastructure.
The higher telemetry settings, specifically “Enhanced” and “Full”, may make it possible for Microsoft to collect business or personal information, since they allow collection additional information when a problem arise with Windows or an app. However, these possibilities are made very clear in Microsoft’s documentation:
If a device experiences problems that are difficult to identify or repeat using Microsoft’s internal testing, additional info becomes necessary. This info can include any user content that might have triggered the problem and is gathered from a small sample of devices that have both opted into the Full telemetry level and have exhibited the problem.
However, before more info is gathered, Microsoft’s privacy governance team, including privacy and other subject matter experts, must approve the diagnostics request made by a Microsoft engineer. If the request is approved, Microsoft engineers can use the following capabilities to get the information:
- Ability to run a limited, pre-approved list of Microsoft certified diagnostic tools, such as msinfo32.exe, powercfg.exe, and dxdiag.exe.
- Ability to get registry keys.
- Ability to gather user content, such as documents, if they might have been the trigger for the issue.
Telemetry data is stored in a hidden folder that is accessible by users, and all the data are encrypted locally (due to privacy activists’ demands) and sent over encrypted HTTPS connections (done since Windows 7 for security.) Below are also several quotes from Ed Bott quoting Microsoft about how the company treat the data transmitted to it.
The data is stored “in a separate data store that’s locked down to a small subset of Microsoft employees in the Windows Devices Group.”
“Only those who can demonstrate a valid business need can access the telemetry info.”
Only “aggregated, anonymous telemetry information” is included in reports that are shared with partners.
Microsoft says its goal is to store data only “for as long as it’s needed to provide a service or for analysis.”
“much of the info about how Windows and apps are functioning is deleted within 30 days.”
Ed Bott has done it again with explaining clearly and concisely how telemetry works in Windows 10, and shows that Microsoft has also been pretty clear on the subject. While there will always be opposing opinions, as Bott said, telemetry is now a part of modern software making that helps make software even better, and Microsoft and Windows is just part of it. The importance is to be informed and understand it for what it is, and you can always count on Ed Bott for it. Thanks, Mr. Bott, for your effort and another great information piece.