The EvilProxy platform operates as a phishing service, targeting MFA-protected accounts, leading to a rise in successful cloud account takeovers. Recent data reveals its widespread use, with researchers identifying over 100,000+ phishing emails dispatched to steal Microsoft 365 accounts.
It uses reverse proxies to execute phishing attacks, intercepting authentication requests and user credentials. Through this, it seizes authentication cookies during login, enabling attackers to surpass multiple security challenges.
Phase 1 – EvilProxy in Action
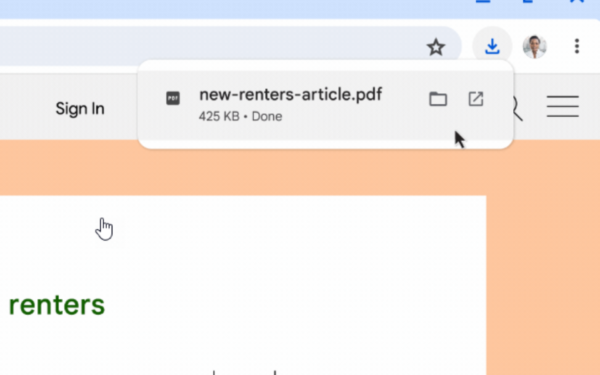
Phishing emails leverage reputable brands like Adobe, DocuSign, and Concur to deceive recipients. Clicking these links initiates a multi-step process, evading detection. Ultimately, victims encounter a counterfeit Microsoft 365 login page, an EvilProxy phishing page.
Attackers evade detection by encoding email addresses, decoding them via compromised legitimate websites, and redirecting users to organization-specific phishing pages.
Phase 2 – Account Compromise
The attackers carefully choose which cases to pursue, prioritizing high-ranking individuals or VIP targets due to their access to sensitive data while ignoring those lower in the hierarchy. Compromised targets include:
- C-level executives.
- CEOs.
- Vice presidents.
- Chief financial officers.
- Employees with access to financial assets or sensitive information.
Attackers may prioritize users based on publicly available organizational information.
Phase 3 – Post-Compromise Exploitation
After gaining access, attackers establish a foothold in the cloud environment. They manipulate MFA via native Microsoft 365 applications. Then the attacker’s MFA method is added post-compromise, ensuring persistent access.
This manipulation includes adding an “Authenticator App with Notification and Code.” They explore lateral movement, study organizational processes, and may engage in financial fraud or data exfiltration.
To counter these threats, organizations should enhance employee security awareness, enforce rigorous email filtering, and consider adopting FIDO-based physical keys for stronger authentication.
via BleepingComputer